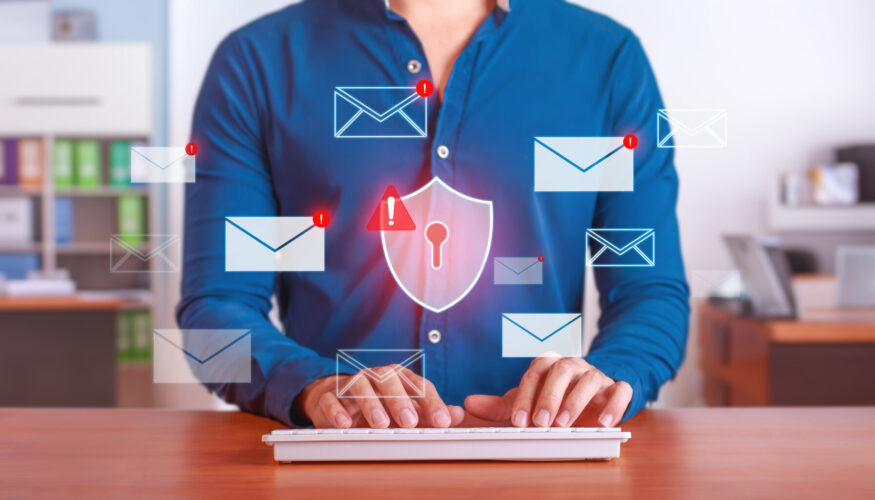
It’s Halloween, which means it’s time to confront all the scary things that can plague our computers and IT systems. A data disaster can strike at any time, propelled by a hack, a virus, a ransomware attack, a phishing attempt, or a social engineering scam.
These terrifying tricks of spooky season can arrive in a variety of ways: malware and spyware that are embedded on your computer after an employee clicks a bad link or visits an illicit website. A single stolen password can be used to infiltrate other computers, accounts, and connected devices. Out-of-date software can be exploited and lead to devastating data loss—something no business can afford.
Like the villain that always shows up in scary movies, these ghoulish problems can seem inevitable. But with good, proactive IT protection, you can secure your information, defend your company’s digital identity, and be the hero who saves the day. Here’s how to protect against a data disaster:
• Surround your systems with multiple layers of security solutions. During horror films, we always scoff at the naïve character who thinks a deadbolt will keep the villain away. The same applies to computers: don’t assume that basic consumer protections will comprehensively protect your business. The right combination of anti-malware, anti-spyware, anti-spam, firewall, encryption, and network analysis tools can construct enough obstacles in the face of bad actors to stymie attacks and keep data safe. Multi-layered cybersecurity solutions are particularly important if you have remote or hybrid employees using computers or devices outside the protective bubble of your office.
• Approach suspicious emails, unexpected attachments, and annoying pop-up ads with extreme caution. Stop us if you’ve heard this scary story before: a naïve employee receives a strange-looking message. Curiosity gets the better of them and they click on the attachment, unleashing a string of Halloween horrors on connected computers, hard drives, networks, and devices. You can rewrite this script by quickly inspecting unknown messages to check the sender address and display name for spoofed domains or sloppy misspellings. Instead of clicking unfamiliar web addresses to see what happens, retype the site you want to visit manually to ensure you end up in the right place. If an email looks like it’s coming from your bank, credit card company, or shipping provider, don’t respond with personal information—instead, call customer service to confirm it’s legit, then mark it as spam in your inbox. And if an infuriating ad keeps popping up, don’t click that viral headline or flashy image just to make it go away. Close the page and move on knowing you made the right call.
• Rely on a trusted IT advisor to automatically install software updates and security patches. You don’t let your kids trick or treat alone, right? Why should you fight off IT demons on your own? A reliable partner like CMIT Solutions can help you avoid the consequences of an outdated operating system or an unsupported program that opens up an avenue for vulnerabilities that hackers can exploit. Our trusted technicians can deploy updates and patches while you sleep, eliminating software-related downtime during working hours and empowering your employees to work faster and smarter on protected machines.
• Use multi-factor authentication on all accounts. Strong, unique passwords might seem like the perfect antidote for a cybersecurity nightmare. But no matter how good you think your password is, remember that hackers can test billions of combinations in seconds, using brute force strength to crack even the toughest code. That’s why multi-factor authentication, which requires you to enter your password and then verify your identity by entering a unique code you receive via text message or email, is equally important. In the case of a stolen password, this can serve as the final obstacle between a hacker and the data that matters to your business.
• Educate and train your employees to be a first line of cybersecurity defense. Cybersecurity education takes real planning and preparation—just like a good Halloween party. Believe it or not, training can even be fun. Set up simulations that test your employees’ knowledge of phishing attempts or social engineering scams. Run ransomware scenarios that time how long it takes for employees to disconnect computers from the network to avoid widespread infection. Hold a competition to see who can spot nefarious emails the fastest. When policies and protocols related to cybersecurity are in place, the people who use them every day are empowered to stand tall in the face of IT ghouls and goblins.
• Finally, the only surefire way to protect computers and the information they store is with data backup and recovery.In case of a Halloween horror, you can always wipe an infected machine clean, restore information from the last backup point, and return to regular day-to-day operations.
If you’re plagued by IT horrors, haunted by cybersecurity threats, or disturbed by regular downtime, CMIT Solutions can help. With multi-layered protection, network security, proactive monitoring, and secure data storage, we keep your computers safe, your data secure, and your systems working smoothly.
Contact CMIT Solutions today to avoid Halloween frights and data disasters this year.