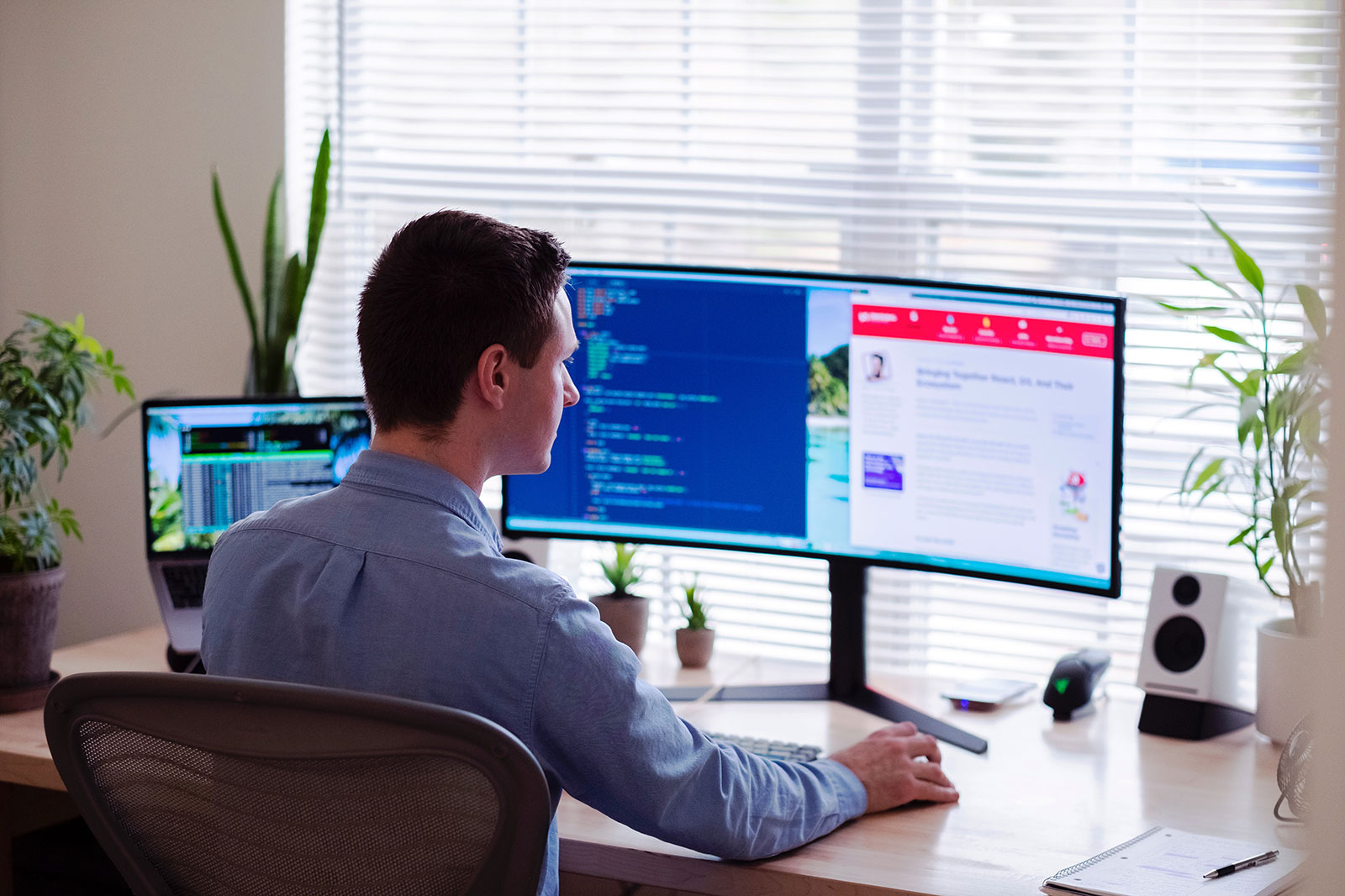
And there I was (as exciting stories often start) sitting at my desk reading through e-mail when a screamer came in … “Antivirus Alert — Threat Detected!”
Our Anti-virus/Anti-malware (AV/AM) software reported that it had stopped not one but two different “trojan horse” viruses attempting to attack a PC at one of our Kenosha-based clients. We got lucky. The AV/AM tool did its job by detecting, stopping, and isolating a malicious virus that would have sat on the client’s PC secretly siphoning off sensitive data like passwords and logins.
These network security threats were known to our AV/AM software and so they were stopped before they could install and do any harm.
While this was a success story, it could have taken a very different path. CMIT Solutions of SE Wisconsin has added three new clients in the last 6 months that came to us because they had a cyber security incident that required an experienced cyber security provider. Each of the three clients had a slightly different tale to tell and, unfortunately, two of the three experienced significant impact to their businesses.
As I debriefed my client, I was struck by the close parallels we are experiencing with the pandemic to information security, cloud security, e-mail security, disaster recovery, and endpoint security. Using our pandemic and the controversy around vaccines is a great analogy here.
When the pandemic first hit we had no test for it, and we had no vaccine for it. We did know that it did bad things to people and that good people were dying. That is what cyber security solution providers refer to as a Zero Day Threat: a new and emerging threat. We don’t know how to detect it and we don’t know how to stop it.

The first thing scientists and vaccine producers did was to identify the The first thing scientists and vaccine producers did was to identify the RNA signature of COVID-19. Once they identified the virus signature, then they went to work on a vaccine to block it. There is a specific genetic signature in COVID that we can detect, just as there is specific code in a computer virus. Cyber security experts refer to this as a virus’ signature.
I’ve written about this frequently in the past and I will continue to spread this message: Good cyber security starts and ends with you. Whether you are protecting your business or your personal information, follow these cyber security solutions to give yourself the best protection available.
Have a good AV/AM installed and running on your device
Anti-virus and anti-malware software is a critical component of your cyber security, and it is the first step in reducing the threat of cyber attacks. However, while Microsoft’s Windows Defender has come a long way in terms of being recognized as a reliable security solution, there are numerous other retail options available for you to consider.
It’s a delicate balance between performance and protection. You want the best protection available without having to deal with the inconvenience of the tool interfering with your work and activities.
Good information technology service providers will also have commercial-grade tools that they prefer to use when protecting the systems of their clients.
You can think of anti-virus and anti-malware tools as your rapid COVID test – they will notify you if you are infected with a virus. Most anti-virus and anti-malware tools, on the other hand, go two steps further than detection. They also quarantine the virus and do everything they can to get rid of it.
Have cyber-security defense in layers
Hackers’ techniques continue to evolve as cyber security experts identify and implement defenses against previously identified attack vectors. A standard signature-based anti-virus and anti-malware system works by comparing incoming files to known viruses.
Unfortunately, these signature-based tools may not be sufficient to prevent a Zero Day Threat from being launched. It is possible that a more sophisticated tool will be required to stop one of these. Fortunately, these tools are available, and many IT Service providers can help you upgrade your company’s protection in order to include this layer of protection. Retail grade products are not always as durable as industrial grade products, but they are improving.

Higher end commercial tools have advanced Artificial Intelligence built in. They use signature based matching for known threats, but they also monitor what a file does on the computer. For example, ransomware signatures will change, but they exhibit common characteristics such as disabling accounts and turning off certain functions before they start encrypting your data and other information.
If an advanced anti-virus and anti-malware tool detects suspicious activity on the computer, it will try to quarantine and remove the virus from the computer, just like it would with a known virus.
Again, there are parallels to be drawn between this and our pandemic. One of the first things that businesses did when the outbreak started was to check their employees for a fever. A fever can be caused by a variety of factors, the most common of which is viruses.
Consequently, if you have a fever, you may be denied entry and required to remain in quarantine until the source of your fever can be determined.
Adopt a zero-trust perspective in all your cyber activities
But what is “Zero Trust”? To have zero trust means that you always assume that whatever or whomever you are interacting with is not legitimate and/or is infected.
If you are in any doubt, follow your instincts and contact the sender via a different method to confirm the message. For example, if you received an attachment from someone and did not expect it, you should call or message them to confirm that they did indeed send you something. If an e-mail contains a link, you can usually find the page or information you’re looking for by going to the website in question directly.
Contactless delivery, curbside pickup, and conducting business over zoom, the phone, and e-mail are all examples of what we can expect in our new pandemic-filled world. We want to keep our contact as limited as possible and only engage in it when we believe it is safe to do so. See our previous articles for examples of how the bad guys attempt to deceive you.
Be vigilant — you are the best defense
There are some excellent tools available, such as those provided by CMIT Solutions of Southeast Wisconsin to our clients. However, these are not the only tools you should use in your defense against cybercrime.
As a result of the pandemic, people are washing their hands more frequently, using hand sanitizers, perhaps standing a little farther apart than they were previously, and – love them or hate them – wearing face masks. These are simple precautions that are equivalent to refraining from opening unknown file attachments or clicking on unknown web links.
Anti-virus protection for humans is very similar to computer virus protection in that it makes use of many of the same principles.
Blocking the virus from entering should be attempted whenever possible; if this fails, look for virus symptoms and take appropriate action if you begin to exhibit any. Assume that everyone you come into contact with, even if you’re protected, has the potential to make you sick, and take as many different precautions as you can to keep yourself safe.If you own a small to medium-sized business and would like to learn more about our security assessments or how we can assist you in protecting your company, contact us today for a free consultation!